Securing automotive software is crucial to life long product security in the field…. But how can you secure a mystery box?
As puzzling as it may be to call an AUTOSAR ECU a ‘mystery box’, this is essentially how many of today’s automotive manufacturers program their ECUs. Over the years, this closed system was enough to ensure total security for these products but that has not kept up with current cybersecurity demands. While there is a strong case for continuing with the AUTOSAR framework, the rise of the software-driven vehicle has created unacceptable cybersecurity blindspots which risk holding back manufacturers from complying with new regulations and bolstering their reputations.
Going forward, the only way for OEMs and Tier-1s to keep up with the ever-changing cybersecurity demands is to have full visibility into all layers of their ECU without exposing any source code to potentially malicious hackers. The first step is to acknowledge this significant cybersecurity hurtles that lie within this proprietary framework. Without full visibility the ability to identify risks and vulnerabilities becomes near impossible, making it tedious to meet ever-changing regulatory requirements.
The next is to find a solution to this product security enigma.
A missing piece to the product security puzzle
Simply put, in order to secure vehicles in line with the latest automotive cybersecurity regulations and standards, OEMs and their suppliers must gain visibility into the makeup of their software. But, that’s easier said than done as many vehicle ECUs are based on the highly popular AUTOSAR framework– one which only approved vendors have access to, yet the entire industry relies on.
While AUTOSAR works for cybersecurity professionals by streamlining processes and industry collaboration, it falls short by not giving visibility into software variations based on manufacturers, needs, and other factors.
This required OEMs to rely on data coming from tier 1 and 2 suppliers, without allowing them to go in and understand the software structure for themselves. Key questions surrounding software components and potential open source code required cybersecurity teams to operate strictly- something that keeps CIPSOs up at night.
To address this, our development team dug deep into the world of AUTOSAR and automotive software to give in-house teams the visibility they demand to secure products both today and decades into the future.
AUTOSAR challenges and industry opportunities
As cybersecurity challenges rise, it’s important to remember that the industry has been far from helpless. Always resourceful, OEMs and tier-1s have relied on various security products to understand their security posture across their full line of offerings. But, gaining visibility into the enigmatic ECU –a place where great vulnerabilities may lie. If developers could illuminate this blind spot, it would allow them to better understand the interoperability between components and develop software and patches as needed.
As black hat attacks on vehicles continued to climb, our task was clear: Enable the industry to drill down from the ECU-level and out to see the full vehicle, understanding the potential risks that may existing within AUTOSAR.
This meant:
- Provide visibility into the software/module composition of AUTOSAR-based ECU firmware.
- Identify and manage vulnerabilities associated with AUTOSAR modules
- Detect any OSS packages (or other) that might be present and any associated vulnerabilities they may have
These have all been achieved by collecting both public and privately reported vulnerabilities both directly from AUTOSAR and our automotive partners.
Integrating AUTOSAR cybersecurity analysis into existing workflows
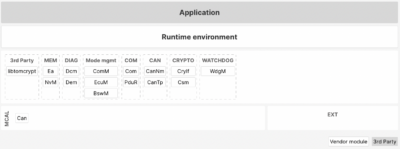
Now, Cybellum’s Product Security Platform can analyze AUTOSAR based microcontrollers (MCUs), identify the underlying modules, present the AUTOSAR architecture, and detect associated vulnerabilities.
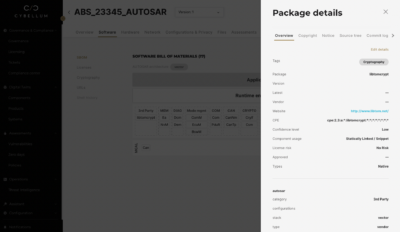
This is all done using familiar visualizations to quickly identify and drill down into specific components and understand its makeup. Additionally, if OSS packages are also packaged as part of the file, they will be detected and presented. Those packages can (obviously) be assessed for any CVEs they may have.
In one example Cybellum’s product security platform helped an OEM identify an unexpected third party application within an ECU. Upon using the Cyber Digital Twin to extract critical information, it was discovered that a software component came from an unapproved third-party vendor. This vendor turned out to not be approved by AUTOSAR, requiring the manufacturer to conduct further analysis to understand if any vulnerabilities existed on this critical component.
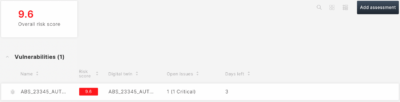
Once a vulnerability is discovered, teams can use the product security platform to visualize the package details, calculate risk scores, and immediately open tickets– reducing friction and ensuring that no vulnerabilities fall through the cracks.
New AUTOSAR cybersecurity solutions in a familiar environment
Delivering greater visibility into the AUTOSAR framework could only be impactful if conducted in a way that is convenient and familiar without adding friction into the development process.
For that reason, we integrated this framework into our product security platform, allowing practitioners to instantly scan their latest firmware to develop a comprehensive SBOM, ensure security against an extensive vulnerability database, and identify any suspicious third-party components that were previously undisclosed.
This level of security works to help companies better understand their components, generate critical analysis and reports around their components, and comply with global regulations, all within an existing framework that is trusted by the industry.
Towards a unified workflow for product security teams
Creating one workflow for product security teams, which integrates with all frameworks and standards, is one of the biggest challenges facing automotive manufacturers. Yet, this challenge is exactly what we set out to achieve at Cybellum.
Our product security platform now integrates with most of the PLM, CI/CD , SBOM, TARA, and Software Update systems, to make product security much more efficient and automated throughout the lifecycle. It then analyzes the cyber risks against more than 60 cybersecurity regulations, to identify specific requirement gaps and allow compliance at scale.
Supporting AUTOSAR is one huge step towards that goal, that will create a whole new standard for automotive cybersecurity around the world.