If you want to see where industry priorities lie — the general consensus is that you should follow the money. Well, between 2020 and 2025, the Healthcare industry is projected to spend $125B on cybersecurity.
There are many reasons driving the attention that medical device cybersecurity is receiving. New regulations such as the FDA premarket submissions and the Software-Bill-of-Materials (SBOM) initiative are top of mind for many manufacturers. President Biden made cybersecurity an essential focus point when he announced his executive order and requested a 14% increase in budget for supply chain and cybersecurity projects.
In addition, cybersecurity is rarely out of headline news, and hospitals and manufacturing lines are an increasing target, as seen in the Log4j attacks — where healthcare organizations were specifically warned to take action against the vulnerability.
Cybellum’s 2022 Medical Device Security Survey Report
Our recent survey, the 2022 Medical Device Security Survey Report puts the maturity of medical device security firmly under the spotlight. We asked 150 senior decision-makers from global medical device companies, all of whom oversee product security or cybersecurity compliance, to be honest about the gaps that they have in their own cybersecurity capabilities. We uncovered the challenges that they are facing every day in keeping their product portfolio secure and compliant as the industry matures and evolves.
Multiple tools and technologies are taking a serious toll
One of the main challenges that was highlighted in the report was the use of multiple tools and technologies to handle various product security tasks, and as a result — fragmented processes. 45% of respondents call a growing set of tools and technologies their top challenge for 2022.
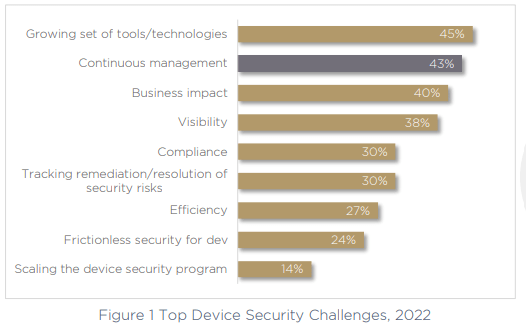
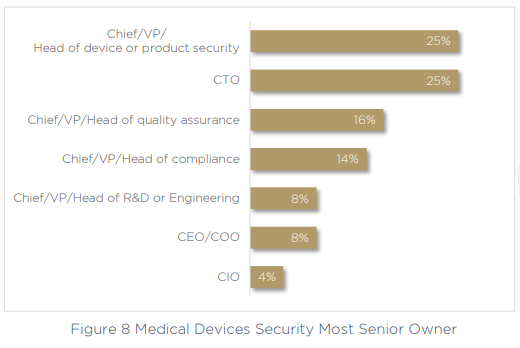
It’s obvious that the more tools and technologies you need to secure devices, the greater the impact on efficiency, visibility and governance will be. Fragmented processes and tools can’t help but slow an organization down, especially when only 25% of companies have a clear Head of Device or Head of Product Security who can take ownership over cybersecurity and compliance. Instead, in another 25% of companies this role falls to the CTO. That’s 75% of organizations who don’t have a stakeholder in this essential role at all.
The challenge of continuous management in medical device security
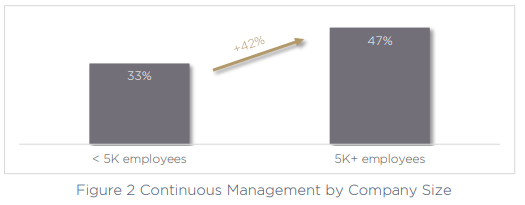
The second-largest challenge for today’s medical device manufacturers is continuous management of device security across the product lifecycle, a key issue called out by 43% of organizations. This can only be exacerbated by the use of multiple fragmented and siloed tools and technologies, making the task much more difficult to perform. Critically, the larger the company, the more of a challenge continuous management becomes.
54% are struggling to shift left and implement continuous management that starts from the design phases of their medical device management, and later in the survey we can also see that 34% call incident response their most exposed area of concern. Clearly, organizations are struggling to shift right as well as left.
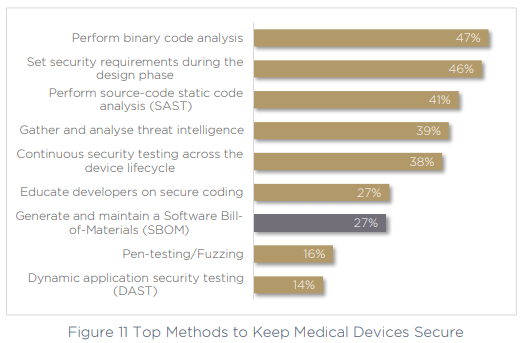
The challenge of continuous management was also highlighted by respondents’ answers to the methods that they are currently utilizing to keep devices secure. 53% are not using binary code analysis to validate their code or uncover vulnerabilities, and just 27% are generating and maintaining an SBOM. Since SBOM generation and binary code analysis are key components of keeping products secure in a continuous way, this is one of the reasons teams may be struggling to manage security continuously.
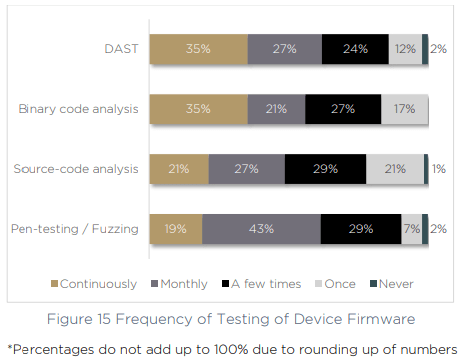
The same gaps emerge when we asked respondents how often they test device firmware. Just 35% of organizations continuously use DAST and binary code analysis more than once per month.
With continuous management across the device lifecycle a growing challenge, and an increasing number of tools, technologies and processes to keep up with — medical device manufacturers are floundering. The risks of complex supply chains, new product lines and a growing number of vulnerabilities are making it an uphill battle to remain secure and compliant.
Many medical devices are not compliant with cybersecurity regulations
These challenges may explain why so many medical device manufacturers are not complying with notable cybersecurity regulations, medical device security standards and best-practices. In fact, we saw that even the most commonly adhered-to regulation, the FDA’s premarket submissions (FDA-2018-D3443) is actually only complied with by 54% of respondents.
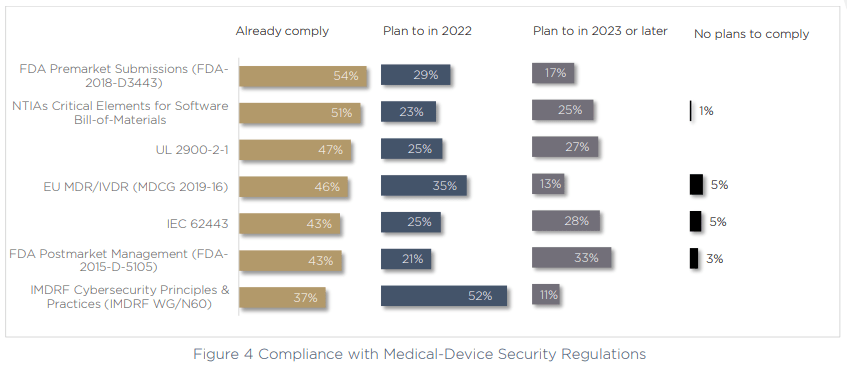
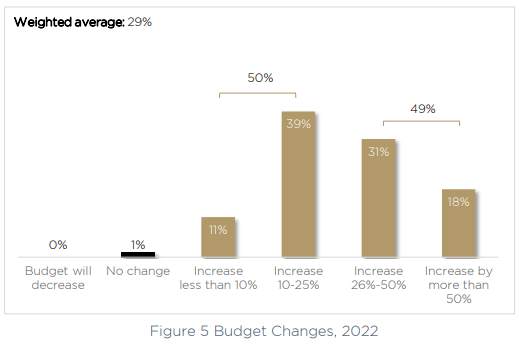
The largest focus for compliance at the moment is with IMDRF Principles and Practices for Medical Device Cybersecurity. More than half of respondents are making meeting their compliance requirements for this regulation a priority over the next 12 months. On top of this, when we asked about why budgets are growing for cybersecurity, compliance was a notable contributor, with 29% of respondents increasing their cybersecurity budget as a result of new regulations.
The truth is, there are conflicting feelings in the industry around compliance. On the one hand, new regulations are catching on quickly — for example the data shows that the SBOM is already complied with by more than half of respondents, despite the directive only being a year old.
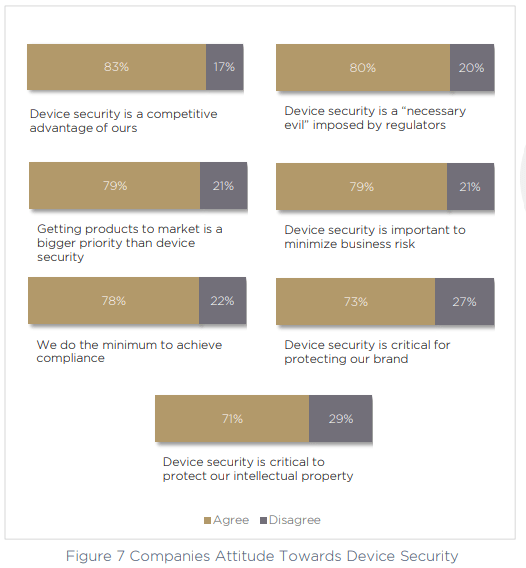
Most of the compliance mandates on our list are on the roadmap for medical device manufacturers within the next 12 months, or shortly after — showing a strong roadmap towards compliance, despite a lack of readiness right now. When we spoke to respondents about their opinions around device security, there was clearly a strong understanding of the impact device security can have. 83% call it a competitive advantage, and 73% call it “critical” for protecting their brand.
However, on the other hand — 78% of companies say that they do the minimum possible in order to achieve compliance, and 80% call out the very idea of device security itself as a “necessary evil” which has the goal of appeasing the regulators and their imposed rules. Perhaps most surprising of all, in 79% of cases, respondents said that time to market for new products and features is more important than device security.
Should organizations be taking compliance, and by association security, more seriously?
Budgets are increasing for medical device security
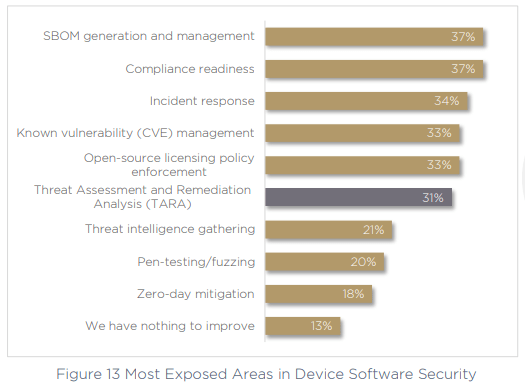
Perhaps the tide is already turning, as respondents seem keenly aware of the most exposed areas of their cybersecurity practices. 37% recognize the problem of SBOM generation and management, and 37% also call out compliance readiness as a problem, almost as many organizations who are non-compliant in the first place. In fact, the third-highest priority for today’s medical device manufacturers is to increase the success of their compliance submissions.
To meet a growing list of priorities, it’s no surprise to see budgets increasing. A larger purse will allow product owners and medical device teams to improve their product security posture. 50% of medical device manufacturers will provide security teams with an increase of up to 25%, and another 31% will see an increase of between 26%-50%. In 18% of cases, the increase in the medical device security budget will be more than 50% compared to 2020.
The growing budget will also allow medical device manufacturers to become more proactive about security, rather than acting reactively — which is the status quo for 61% of companies post-production. That’s almost two-thirds of companies who are failing to prepare ahead of time for their incident response or the realities of a cyber attack on medical devices.
Are medical device manufacturers ready to face a cyber attack?
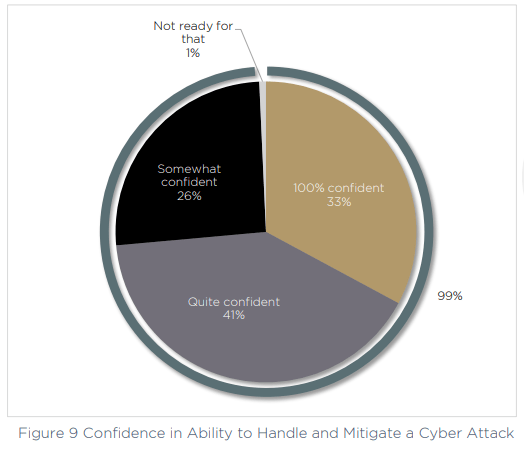
Improving incident response and readiness for a cyber attack may be even more important than organizations think. We found that medical device manufacturers may be wildly overstating their abilities to fend off a cyber attack, or are perhaps in denial about their capabilities, or failing to connect the dots. This is backed up by the data, which shows that the same respondents who display high levels of confidence in their ability to ward off a cyber attack have also identified critical gaps in incident response and cyber defense programs.
First let’s look at the confidence levels, which are extremely high within the survey respondents. More than one third are “100% confident” in their ability to handle and mitigate a cyber attack, and a further 67% are “quite” or “somewhat” confident. That leaves just 1% who say they are currently not ready to face an attack.
Compared to the competition, respondents also feel supremely confident in their preparedness. Just 5% believe their competition is better prepared for a cyber attack, and almost a third (32%) saying they are much better prepared than other companies in their field.
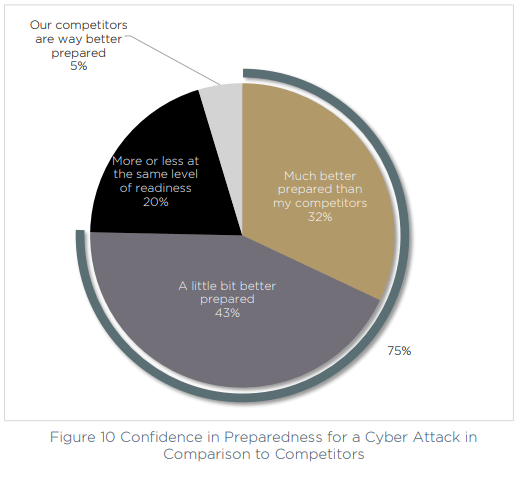
Interestingly however, as presented above, the evidence stacks up against this point of view. If we look back at figure 13 above, we asked respondents for their most exposed areas of concern within device software security, and 34% called out incident response, while a further 31% mentioned TARA (Threat Assessment and Remediation Analysis). Without these core capabilities dealt with — how prepared can an organization really be? Without assured, tried and tested incident response, this confidence is clearly misplaced.
The industry has a way to go, but MDMs are on the right track
The most hopeful message we can take out of our 2022 survey is to look at the challenges we’ve uncovered side by side with the priorities on the product security product roadmap over the next 12 months and beyond.
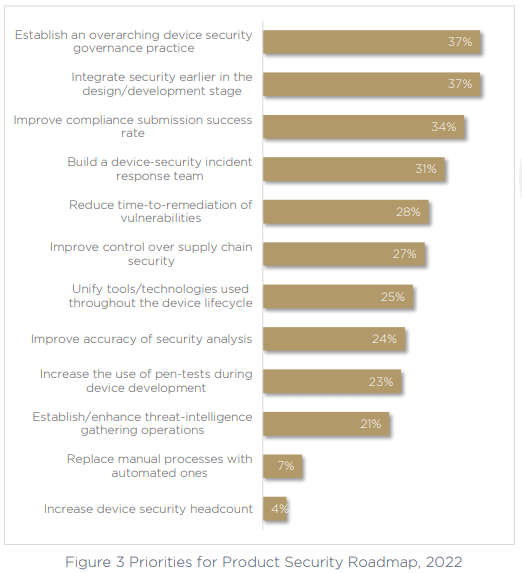
Top of the list, with 37% of respondents calling it a priority is to establish an overarching device security governance practice. The 75% of respondents who don’t have a clear stakeholder in charge of this critical area of the business are looking to make a change, and the growing number of technologies needs to stop, consolidating tools into a more manageable workload that offers greater visibility.
Next, the same number of respondents are focused on fixing the ongoing issue of continuous security management — shifting left on security to bring it earlier in the design and development phases. This will allow teams to act with more proactivity, and have security implemented way before production, without impacting time to market — a priority that’s not going anywhere in today’s world, which has a growing emphasis on the lightning-fast product-release cycle. Shift left means happy developers, happy security teams.
Third on the list of priorities is to improve the compliance submission success rate. This is an obvious necessity as we have seen that only half of respondents are currently compliant with the necessary medical device security standards and frameworks, and the top exposed area is generating and handling SBOM.
Finally, and also a top priority for more than 30% of respondents, building a specific device-security incident response team. The inclusion of this priority suggests that organizations are not as confident as they may seem. Recognizing their gaps, exposed areas, blind spots, and the maturity levels of the industry — medical device manufacturers realize they have a long way to go, and are ready to do the work to ensure their product portfolios are secure and compliant.
Cybellum helps product security teams make their products secure for life. With Cybellum’s product security platform, teams manage security across the entire lifecycle of the product, whichever new threat arises. From living SBOMs updated with every change, to automatic vulnerability management and ongoing incident response, teams can keep their entire product portfolio secure and compliant at all times.
Let’s talk about what we can do for your medical device manufacturing organization? Schedule a demo so you can see how the platform works for yourself.