This week, major US government agencies, including all five branches of the US military, the Pentagon, 425 of the US Fortune500 companies and other organizations across Europe, Asia and the Middle-East, discovered their IT networks had been breached by hackers looking to steal sensitive data (the identity of the intruders is still not clear).
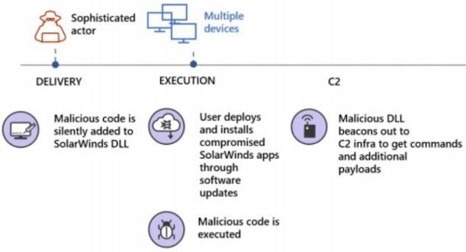
The attack was carried out through a months-long operation against IT technology vendor, SolarWinds, that had supplied the hacked companies with its Orion Platform for network monitoring and management.
The backdoor for the attack, dubbed SUNBURST by security vendor, FireEye (which was also hit by this attack), propagated to 18,000 SolarWinds customers via the Orion Platform update server, which according to some security researchers, could have been accessed by anyone, using a password published on SolarWinds’ public Github repository for over a year.
Once on the update server, the backdoor was distributed via automatic update to platforms or systems in target networks.
credit: HELPNETSECURITY
So far, it appears the attack was used for espionage, but since some SolarWinds clients were infrastructure operators, it could have been used for sabotage as well.
It will take a while to fully understand the depth and breadth of this supply-chain attack, but it’s already clear that this was a very sophisticated operation on a grand scale, targeting the soft-belly of governments and enterprises – their supply chains.
This event, and others that preceded it (anyone remember NotPetya from back in 2017?) serve as wakeup calls for the public and private sectors to double down their efforts to secure their software supply chain.
But they are not the only ones that should be concerned.
Imagine what would happen if attacks were launched on the complex supply-chains that support the development of products such as consumer IoT devices, connected vehicles or medical devices. The risks are even higher – operational risk to equipment, privacy risk to data and safety risk to the well-being of people.
Product development and manufacturing supply-chains, especially those involving software, with their abundant use of 3rd party code of a commercial and open-source nature, are complex and somewhat invisible. It’s very difficult to see into their make-up and characteristics, which also means that cyber threats, accidental or intentional, can lurk within.
The Ripple20 vulnerabilities discovered in June 2020 – though probably not a deliberate attack – demonstrate the risk with software supply chains security.
OEMs and their suppliers must become cyber-responsible if they are to secure their future business and their respective customers. Fail to do so, and they risk unsustainable exposure to regulatory violations, liability claims, brand equity erosion and more.




