A guest blog by Mr. Tetsuya Mikami, Senior Manager at Deloitte Tohmatsu Consulting LLC.
I imagine that whoever just started reading this article is in charge or has a high interest in cybersecurity in the automotive industry.
How are you positioning cybersecurity in the automotive industry? Is it a feature? A service? A regulatory requirement? Safety or security issue? Quality or performance issue? In-vehicle feature? A job function of some department? Or something to be addressed by the whole company?
Positioning differs depending on the geography and the type of organization. However, “risk” is something common among them. A cyber threat increases the “risk” of loss or damage to vehicles, users, OEMs, suppliers, sales companies and dealers, mobility service providers, and any related stakeholders in the automotive industry.
As part of risk management, the idea of creating cyber threat countermeasures has gradually spread across the globe, especially in the US and Europe.
One of the major trends I see now is to become compliant with WP.29 (UNR-155/156) regulations, which will impact type approvals. WP.29 is planned to be effective from July 2022 starting with OTA equipped new models in Japan.
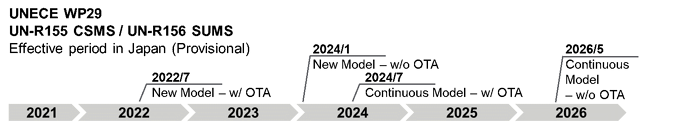
Considering that the regulation will gradually become stringent, it is time for the automotive industry to build continuous risk management, rather than to comply with new automotive regulations in an ad-hoc manner.
Environmental Changes and Increased Cyber Risk
The automotive industry is facing dramatic changes in response to various green initiatives and requirements such as electrification for carbon neutrality, promotion and use of autonomous cars, sales model transformation, and supply chain transformation.
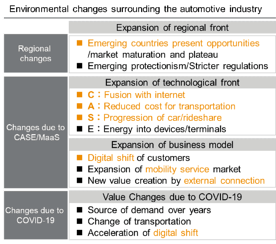
In-vehicle software is undergoing a phase of major change in response to environmental changes. The current number of LOCs (Lines Of Code) in a vehicle has reached 100 Million and the numbers are likely to reach 600~700 Million LOC by 2025.
Not only is the number of LOCs increasing, software structure is changing as well – we can see that from recent OEMs’ effort put into the development of vehicle OS.
Connected features are getting more and more complex and functional improvement/expansion frequency by OTA (over-the-air updates) will also increase, which will invite new players to the automotive industry like IT and telecommunications.
As connected functions get enhanced, V2X (vehicle to everything) communication will become a standard, which may likely redefine the term vehicle safety. Unfortunately, it may increase the likelihood of cyber attacks. Connected features may increase entry points and more software will have to be secured. From the standpoint of cybersecurity, the automotive evolution will increase the overall cyber risk.
Cybersecurity will, therefore, become obligatory as automotive design advances.
The Automotive Industry is Facing Cyber Risks
Talking of cyber incidents in the automotive industry, the most famous one I believe is the so called “Jeep Hack”, which made FCA recall 1.4 million vehicles. Since then, few incidents have appeared in the news, however in real world, the number of incidents is increasing.
The number of incidents has increased more than six-fold over the past 5 years with hundreds of incidents now occurring every year. Looking at the types of attack in 2020, 77.8 % of them were remote attacks and 49.3% were blackhat style attacks. These include fleet-wide hacking targeting multiple vehicles. These cases succeeded in the fraudulent operation of vehicle control systems and collection of user’s personal information from the vehicle.
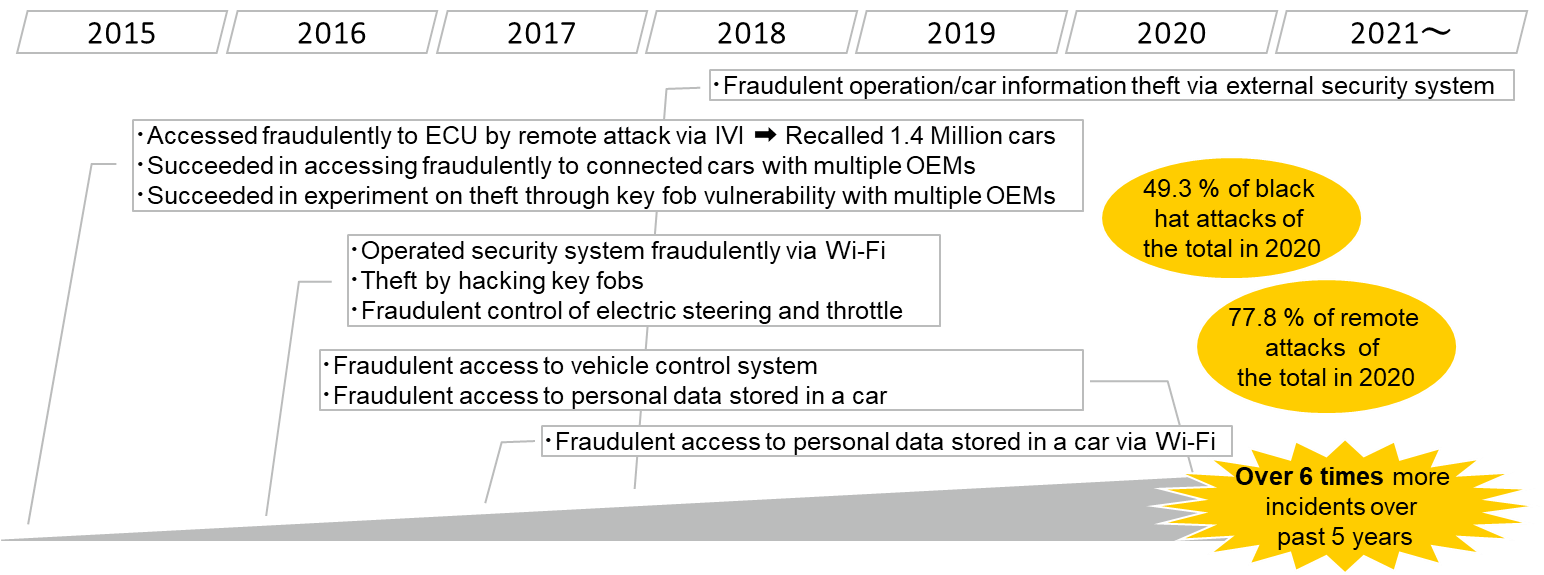
All cyber attacks have something in common – a “vulnerability” is always the starting point. An “open port” in the IVI (In-Vehicle Infotainment) system as being the vulnerability was the root cause for the Jeep hack incident.
When it comes to software with over 100 Million LOC, attackers are not building exploits by relying on their intuition. Instead, they identify the vulnerabilities in the first place and build exploits to target them.
There are numerous vulnerabilities disclosed to the public. Vulnerabilities continue to increase by ten-thousands every year while the CVE (Common Vulnerabilities and Exposures) database already has more than 150,000 known vulnerabilities registered.
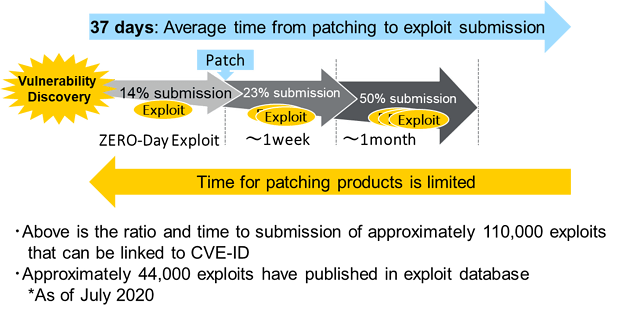
Additionally, over 44,000 exploits can be found in Exploit Database. Exploits against approximately half of the vulnerabilities found will be built and published in under a month from their discovery. Conversely, impact analysis to “complete product lines”, patch creation and distribution to all the parts that may get affected, must be completed within a month.
Taking proactive measures against cyber threats is the only effective defense.
Dealing with vulnerabilities is also a compliance issue. UNECE WP.29 (UNR-155/156) requires vehicle risk management throughout the entire vehicle lifecycle and for monitoring, vulnerability management is required.
However, automotive cybersecurity measures are not just a story of complying with the law or regulations. Companies involved in connected cars as well as users are all exposed to cyber threats. Companies need to put in place measures to mitigate the risk against cyber threats. Considering how rapidly cyber threats evolve, we must assume that the time allowed to implement cyber risk measures will become shorter and shorter.
Preventing Cyber Risks
I have communicated with many people from various positions in the automotive industry, that are involved in cybersecurity. I feel that Japanese tend to capture cybersecurity as a “technological issue”. Seemingly many of them consider that the product will be secure as long as they have a robust design against cyber threats.
Of course, technology is a key aspect, and securing design, implementation and evaluation is important. However, cyber risk measures must be continuous and must cover the whole lifecycle of the vehicle.
Functions that were completely safe yesterday could have vulnerabilities today, and the risk of a possible attack may suddenly and dramatically increase. This is the nature of cybersecurity.
Since the vehicle development cycle for a new model generally takes 3 to 4 years and facelifts (the shortest vehicle development process) will typically take a year, we must consider that cyber threats have evolved from the vehicle’s design to its launch.
Therefore, security must be ensured on the day of launch and must be continuously assured thereafter. As Figure 5 below demonstrates, to do so, a dedicated system and process as well as a monitoring environment will be needed.
This allows remediation of product vulnerabilities discovered during continuous monitoring. To catch all potential cyber risks, any software component accessible from outside the vehicle must be monitored.
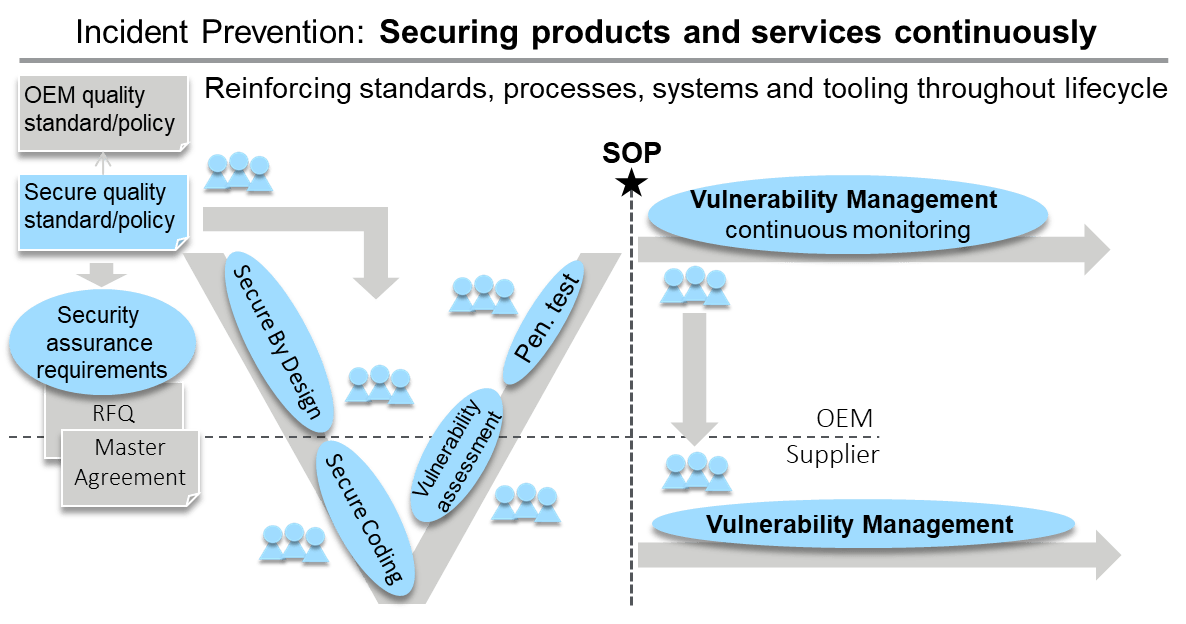
Secure vehicle development requires all OEM departments and suppliers involved in vehicle, feature and service development to guarantee the same level of security. OEMs who are responsible for the vehicles, must set a quality standard defining what is “secure”. Quality standards are established for hardware or key features like passive safety, NVH and durability and also for key software capabilities like control, IVI and digital cockpits.
So what about “performance/quality standards” related to cyber threats? Are there any clear standards defined? For example – in the Ecommerce world, system performance/quality standards define the security for user transactions.
Nowadays, users have grown up in a digital world using smartphones and computers from their childhood. They will definitely expect the same of level of security for their vehicles, especially as in-car transactions are becoming standard.
Standards for mobility services will also need to be established. Drive recording might be falsified for telematic insurance services; mileage or fuel/battery levels could be falsified in car sharing services.
Considering the fact that more actuators will become electronically controlled, unmanned vehicle theft maybe possible, whenever level 4 autonomous driving is achieved. Clear and secure quality standards and policies are required to ensure the security of vehicles, features and services.
OEMs must implement standards and policies throughout the vehicle development. Globally, many OEMs are now working to enforce their security policies, which I consider to be still immature and evolving.
I see a trend, mainly coming from Europe, to move development in-house. One of the reasons is to keep the competitive technology and strategy under control, but another reason is to enhance security-by-design.
Part 2 of this blog series can be found here.