Manufacturing companies are huge enterprises with multiple business units and vast product lines. This means managing product cybersecurity and ensuring cyber compliance is nearly impossible. With such a big organization, how can managers quickly pinpoint the risks that will have the greatest impact? How can you know which team needs your immediate attention or which supply chain vendor is posing the most risk to your business?
The answer, it takes a village to properly begin understanding a product’s cybersecurity posture and analyze the potential business impact should a vulnerability be exploited- and that’s only for one device!
Product security is a relatively new practice without tools that present the full organization-wide security operations. This leads to managers juggling multiple business units, each managing various projects, which in themselves have multiple vendors, complex components, and endless lines of code. Beyond meeting cybersecurity policies, whether set internally by the organization or through government regulations, each security team focuses on different data points to understand their product and keep it secure against sophisticated malicious actors. As vulnerability teams focus on mitigations, compliance teams will be preoccupied with remediating regulatory violations.
While everyone is focused on their task at hand, managers quickly fall out of the loop and may spend their day trying to play catchup across teams and product lines.
For these reasons, Cybellum’s platform surfaces timely information across teams, business units, and supply chains. The main dashboard displays the data that matters most to each department so managers, from security, legal, compliance, and beyond receive the most relevant information needed when drilling down into the details.
Now managers can review product vulnerabilities, pinpoint weaknesses in the supply chain, and review the status of legal compliance in one easy to use dashboard.
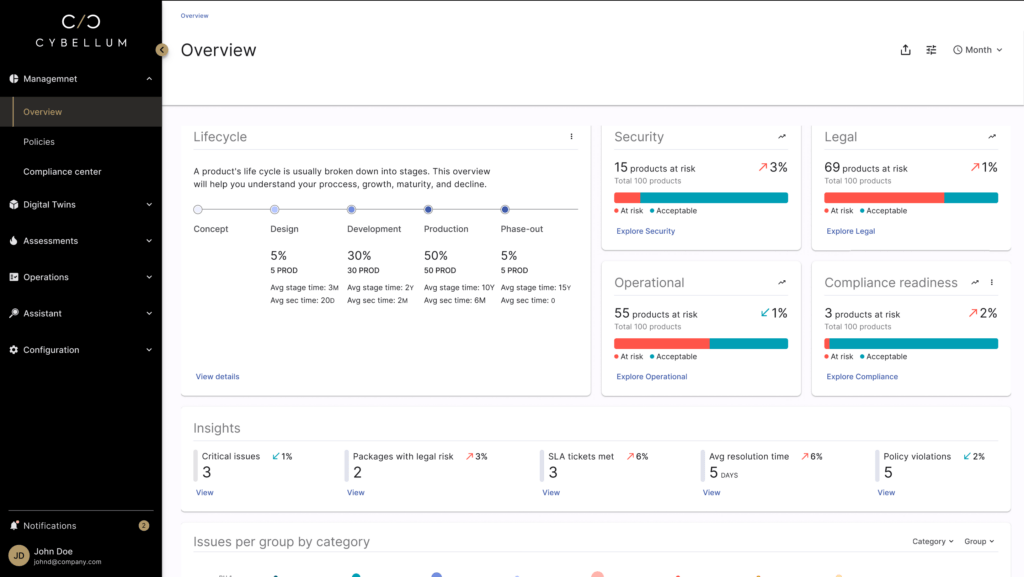
Critical insights are front and center, allowing for better oversight. Image: Cybellum Product Security Platform
With a simple secure sign in, authorized users are greeted with a full rundown and status of what matters most to them. What’s more, this birds-eye view dashboard gives a breakdown of critical insights above the fold while giving access to risks per group based on business units, customers, teams, locations, and more.
Quickly securing the supply chain
No one can escape the disruptions that companies across industries have experienced due to shake ups in our global supply chains. In an effort to keep product deliveries on schedule, many organizations have begun looking for new vendors who are able to meet demand while maintaining a high level of quality.
The challenge here is understanding what kinds of risks exist by partnering with new companies and visualizing risks that may find their way into products. With a dashboard focused on rapidly and accurately delivering critical information, managers can view their full supply chain to identify the riskiest products and vendors, mitigating risks before un-secured software components find their way onto customer networks.
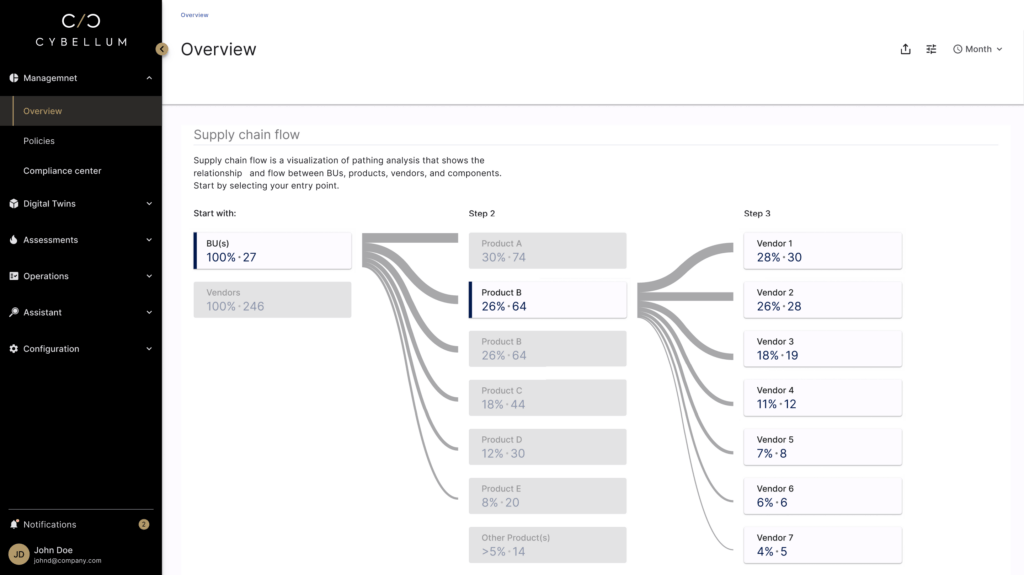
Visualize your supply chain flow to manage security across business units and their vendors. Image: Cybellum Product Security Platform
Defining software policies and security
Understanding your products’ risks goes beyond protecting against cybersecurity threats. Other challenges that may arise are compliance standards, software licensing, and internal metrics.
Using the management center as a single source of product security management, managers can define policies associated with regulations, standards, or according to an internal metric. See which products or teams are using them, and track any gaps you may have across all product lines to gain deep insight with a glance.
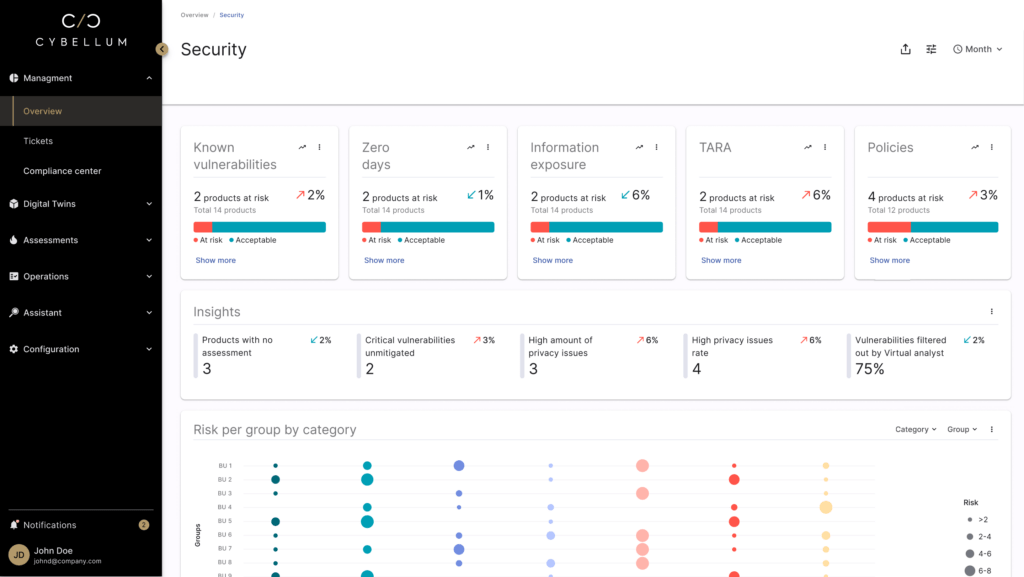
The Security dashboard tracks critical metrics over time and tracks top-priority tasks back to their team. Image: Cybellum Product Security Platform
Expanded KPI capabilities allow you to remain in the know- so decisions can be optimized, based on the latest data. These include insights regarding CVEs, vulnerabilities, privacy issues, zero day vulnerabilities, and policies that are only related to security.
Beyond security with operational insights
Being an impactful product security manager demands the ability to quickly identify the most critical issues across product lines and business units. It is equally important to know when a component displays the greatest risks, how to prioritize mitigations of the identified risk, and how to keep products securely in the field.
The Management Center will give you a rapid glance into understanding which components are due for review while also giving you insight into the average time to close tickets. Now, managers can conduct predictive maintenance based on data.
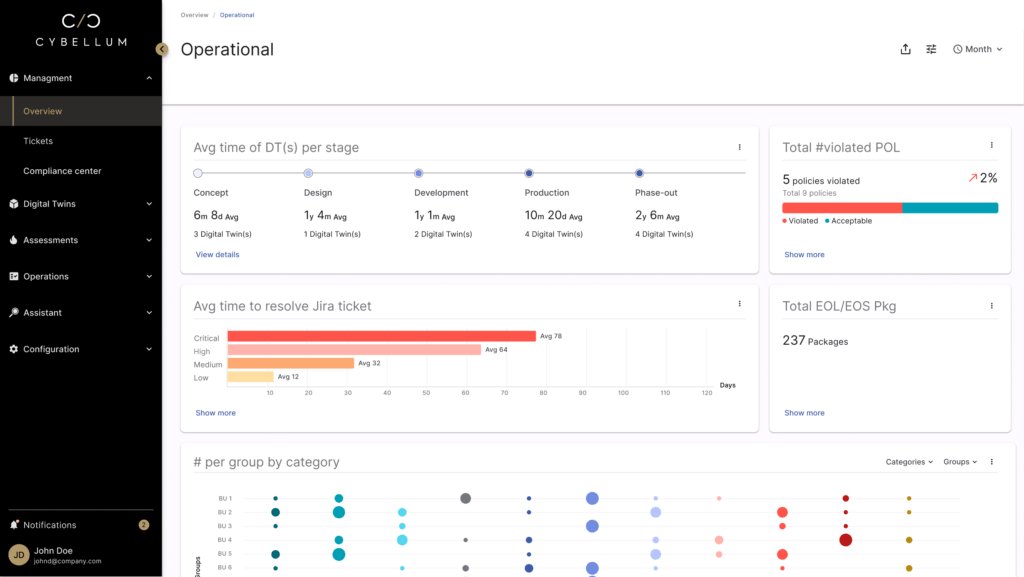
Gain a panoramic view of your operations, allowing you to understand products throughout their lifecycle. Image: Cybellum Product Security Platform
Finally moving away from a reactionary mode to a full dashboard-driven overview allows for better resource management, from initial design and development through end of life decommissioning.
Maximizing product security resources
Today’s cybersecurity teams are tasked with meeting a seemingly never-ending flood of alerts and risks that are looking for the smallest vulnerability in order to carry out a catastrophic attack. Even with increased support over the years from executives, cybersecurity team leaders must maximize every resource available or risk a weakened product security posture.
By utilizing a management-focused dashboard, practitioners can make faster decisions, continuously track mitigation status, and dynamically allocate resources, freeing up time to handle other tasks and plan for the future. This frees up time and resources, allowing talented security teams to manage the full development process from start to finish.