Red Team Automation
Detect, validate and mitigate coding weaknesses in proprietary and 3rd party code, leveraging smart automation
Product Red Team Automation
Become a Zero-day machine
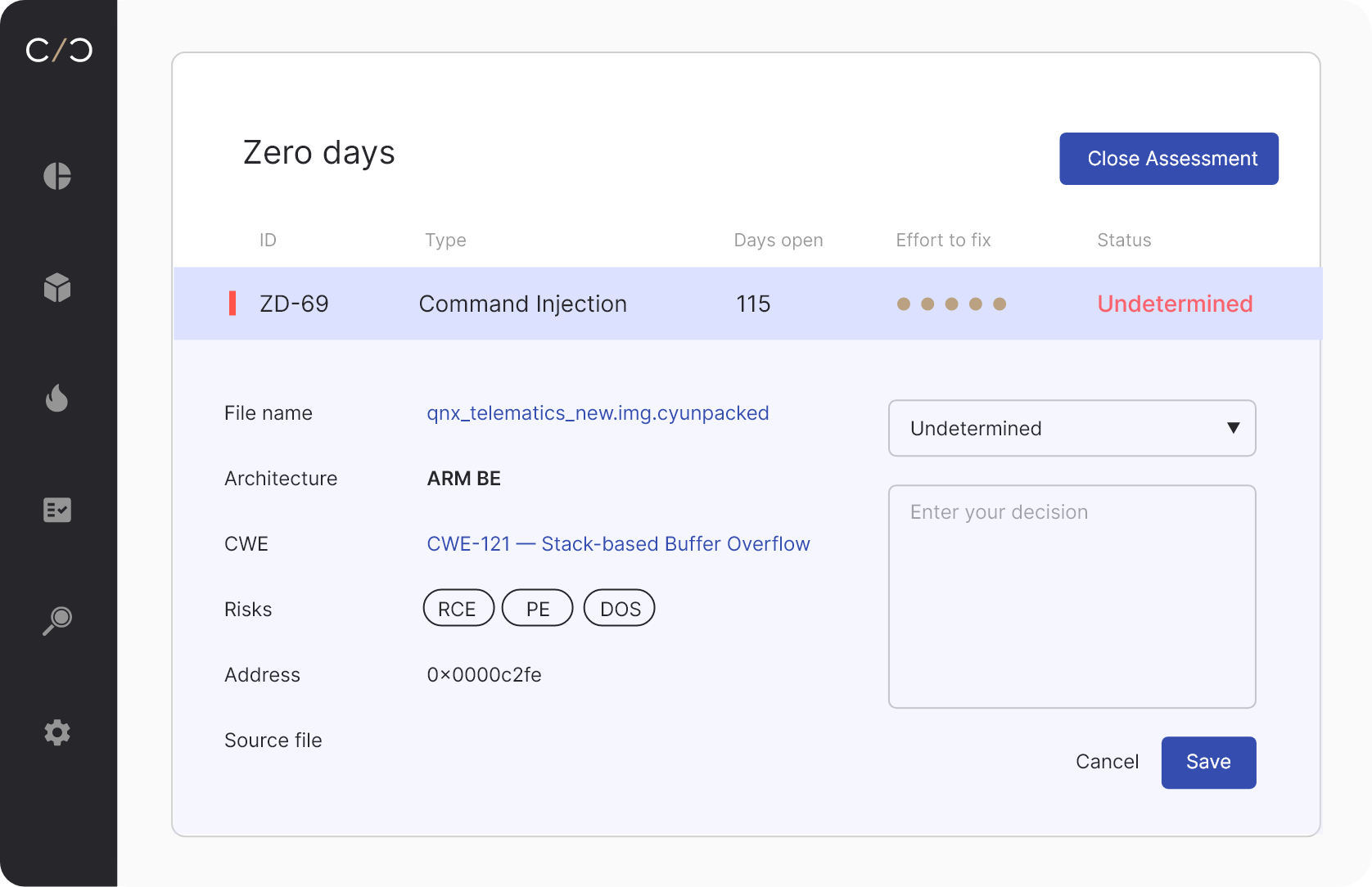
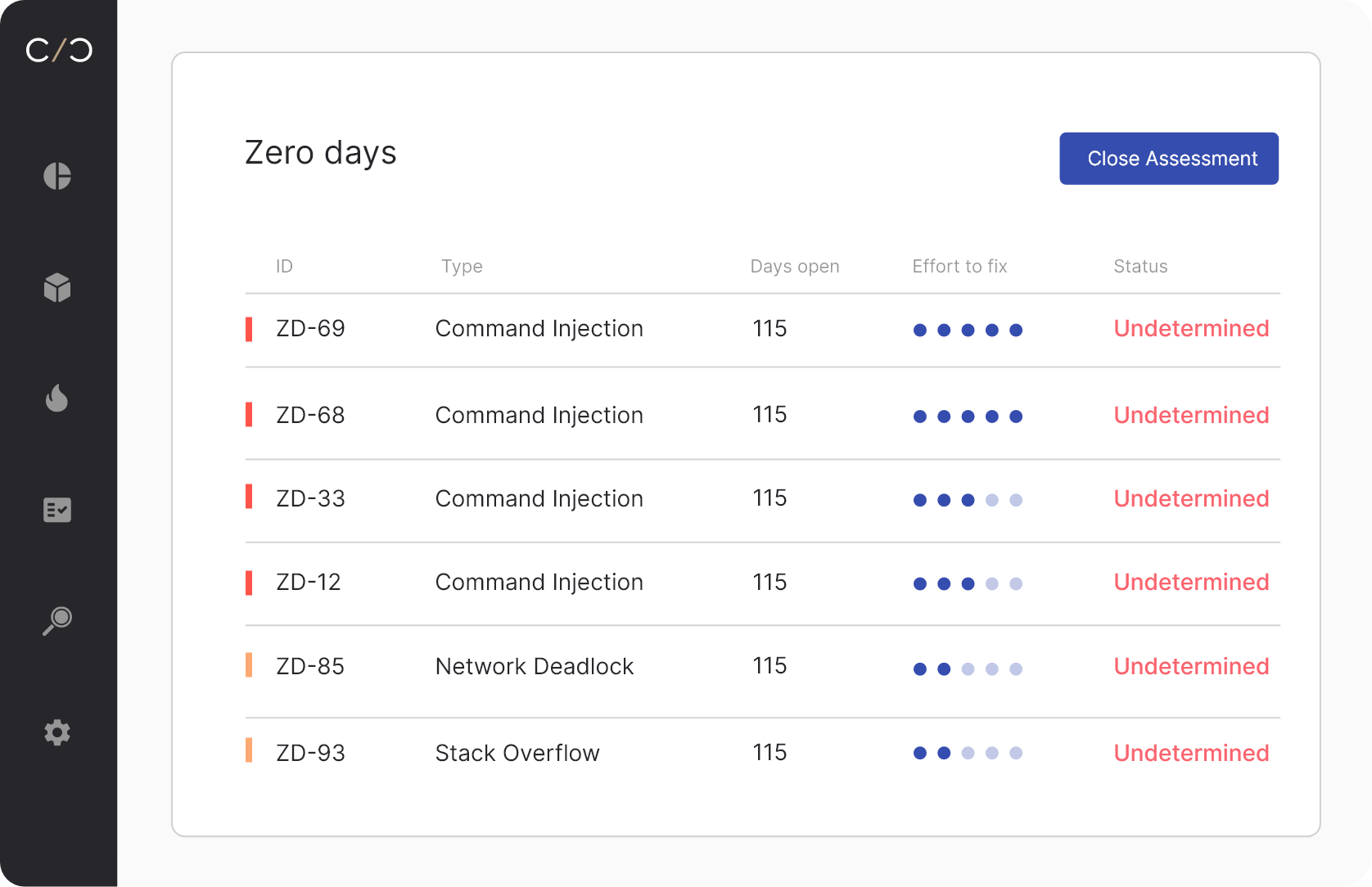
Automate workflows
Get from coding weakness detection to mitigation, across all product lines and versions by leveraging workflow automation
Validate dynamically
Use a dynamic validation engine and leverage existing SBOM data to greatly reduce false-positives
Analyze across the board
Conduct analysis regardless of the platform, with support for multiple CPUs and MCUs
Give your red team superpowers
01
Automate
Automate
your operation
Scale by automating a large portion of the red team process
02
Stay compliant
Comply with relevant regulatory requirements
03
Enhance product
Enhance product
security
Make sure products are secure before they get to market

Cybellum’s platform allows the team to detect and mitigate risks early and often
Supermicro’s software security team
Other Product Security
Platform use cases
BU 1
BU 2
BU 3
Threat Modeling
PLM/ALM
SBOM Tools
CI/CD
Ticketing Systems
Threat Sources
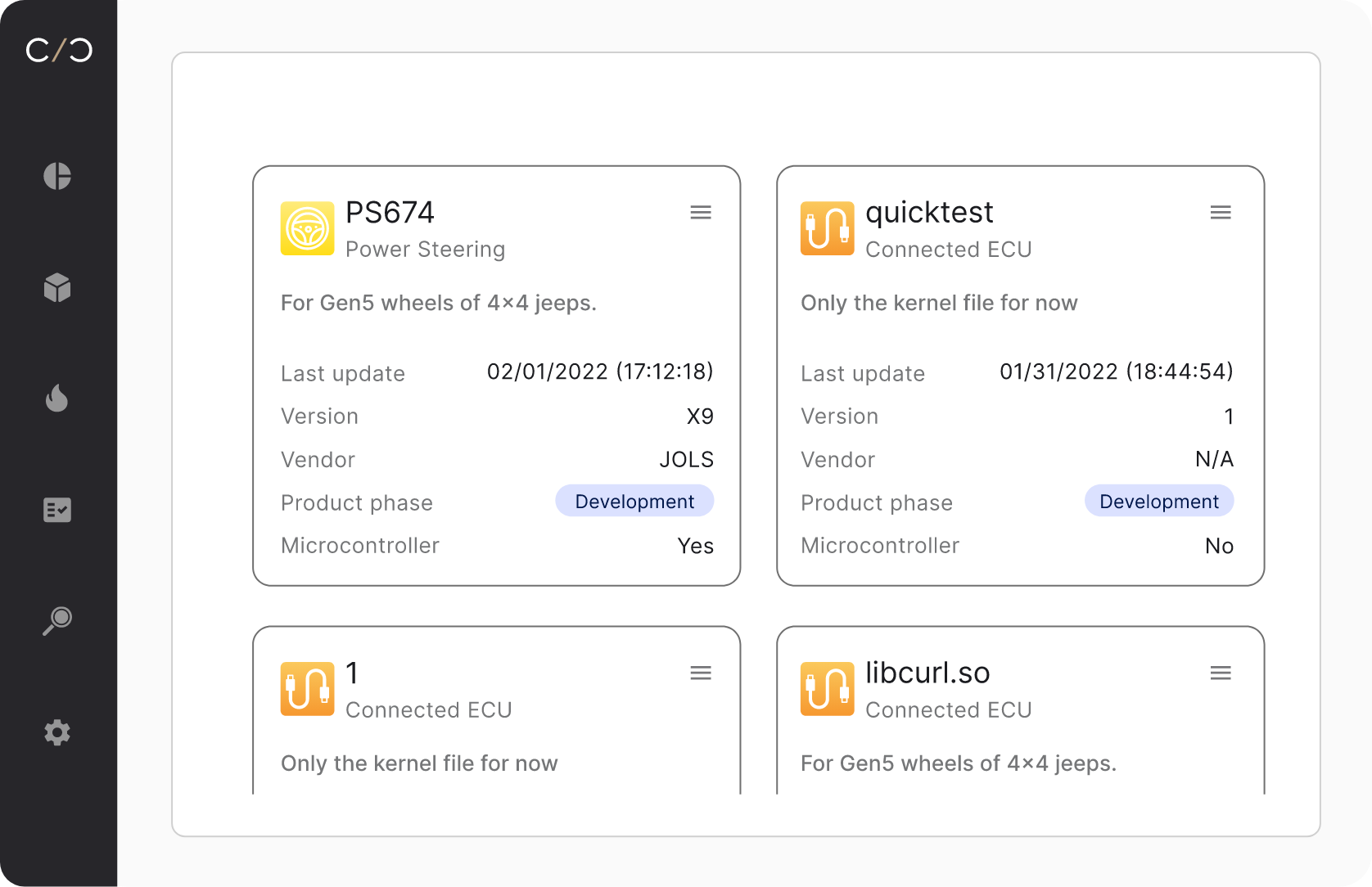
Software Updates