Overview
This is Part 2 of our blog series reviewing ENISA’s report on the importance of cybersecurity for connected cars. Continuing from where we left off in Part 1, in this blog we will cover the organisational practices.
To receive more content on automotive cybersecurity, follow us on Linkedin.
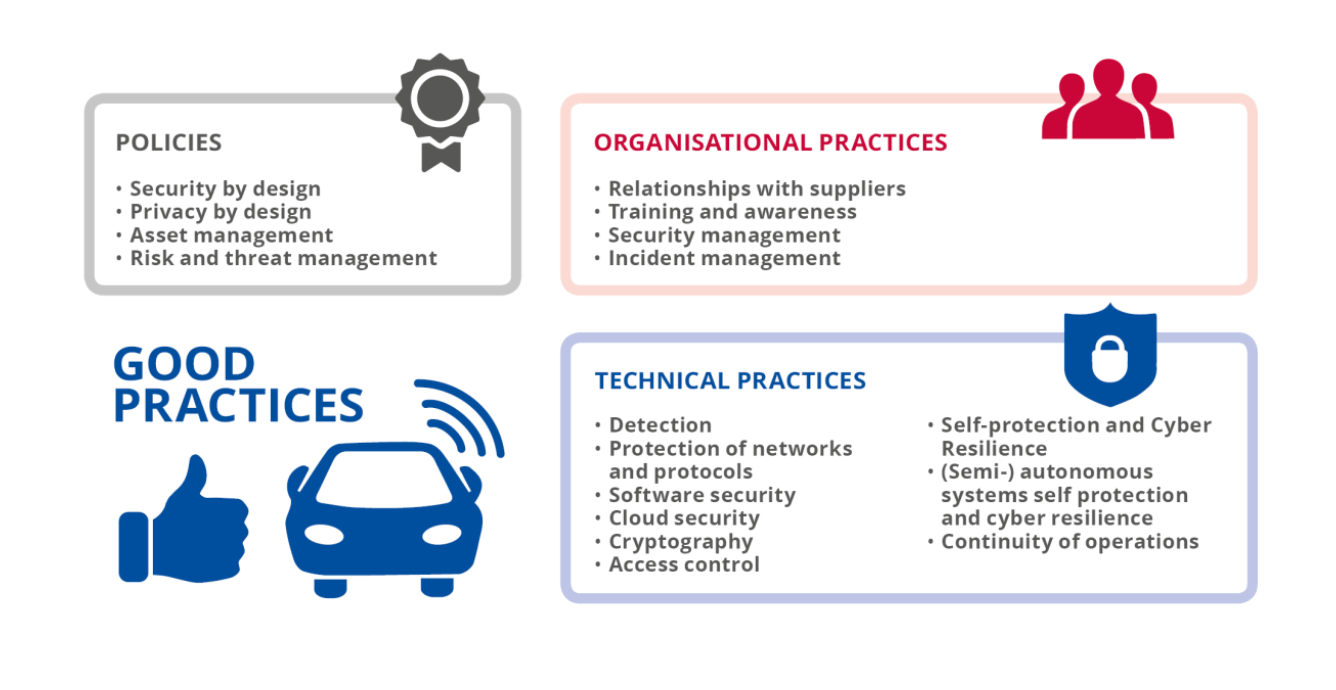
Organisational Policies
The report provides organisational practices guidelines in four categories:
- Relationships with Suppliers
- Training and Awareness
- Security Management
- Incident Management
1. Relationships with Suppliers
The guidelines call for “security-related information sharing” (guideline OP-01) and cybersecurity “along the supply chain” (OP-02). However, the means to meet these guidelines are left open, since there are no clear standards on how this should be met.
2. Training and Awareness
Relevant information should be shared between all parties involved (OP-03). The model of Information Sharing and Analysis Centers (ISACs) is mentioned specifically. Employees and suppliers should be trained (OP-04), continuously and regularly (OP-05). The public awareness of security issues and prevention methods should be increased (OP-06).
The challenges for the industry as we see them are in practical and acceptable methods of sharing cybersecurity information in an industry that is now used to not share information at all. OEM cyber experts today receive pre-production units without any notion of the device internals, and when issues are found, the reporting is heavily filtered before it comes back to the supplier. The industry has to “open up” entirely from its current operational mode.
In addition, the public awareness is lacking since vendors have mostly avoided cyber security – meaning the protection against threats, as a promotable safety mechanism. OEMs are not reporting their efforts in this regard to the public. Arguably, the public is not knowledgeable enough in many cases to fully understand the technologies behind either the risks or the mitigations.
Another angle is the information sharing and education. Finding vulnerabilities is not enough. Risks must be presented as actionable results, with the necessary explanations and mitigation steps.
3. Security Management
The report recommends OEMs to establish a SOC (guideline OP-07), and define an “Information Security Management System (ISMS)” that covers the entire lifecycle of vehicles (OP-09). In addition, it calls for the obvious implementation of designated security teams (OP-08) and strategic task force (OP-10).
Unfortunately, there is currently no explicit definition to an OEM SOC (or as some call it, VSOC – Vehicle SOC). The same goes with ISMS (which some call CSMS – Cyber Security Management System). As in many other cases, when there is a void, commercial parties come up with appropriate solutions.
4. Incident Management
To meet ENISA’s guidelines in the Organisational Practices category, a solution must:
- Serve as a central management for the cybersecurity relationship across the supply chain.
- Enable practical sharing of cybersecurity information between all parties.
- Support PSIRTs and CSIRTs in their day-to-day security operations.
In addition, the vendors involved must promote the information sharing, so ideally, a solution should support the distribution of this information to both internal and external parties.
In Cybellum, we are working on such a solution. Already today our products promote the sharing of security information. In addition, we are closely following the industry’s reaction to the information sharing related guidelines, and we expect to evolve towards that direction.
Organizing Cyber Security with Cybellum V-Ray
V-Ray serves as an CSMS (or ISMS as related in the guidelines), providing a central access point to security and risk information for both automotive OEMs and third-party suppliers alike. Access is controlled so each party can only manage and review its relevant information.
The result is an open (yet secure) infrastructure for automotive cyber security, whereby parties can identify and share details on risks and mitigation steps with others. In other words, Cybellum Security Suite is built for a future where security sharing will be the common modus operandi, but already support today’s supply chain vendor/supplier operations, where information is typically not shared through common systems.
For a demonstration of how Cybellum Security Suite can change how your organization performs software risk assessment, contact us.
Stay tuned for Part 3, where we will cover technical practices. We will review a variety of guidelines covering detection, protection and security controls aspects. In addition, cryptopgraphy, software and cloud security guidelines will be reviewed as well.