Before we go ahead and say goodbye to the internal combustion engine (ICE) Porsche Macan in 2024 due to (spoiler alert) not meeting WP.29 standards, we will still see its electric twin on the roads of the EU.
Perhaps while not identical to the ICE Macan, the electric version is built upon VW Group’s PPE platform, which brings a component approach to electric chassis and reduces the development time of a vehicle. This electric Macan is most likely WP.29 R155 ready, meaning that critical automotive product security steps have been taken to ensure safety and reliability well after it rolls off the production line.
However, there is something profound to be said about the removal of the Macan. For one, it is a loss for those who appreciate the performance and mechanical beauty of ICE vehicles. The inability or unwillingness to bring the Macan up to the latest compliance standards is a bold statement that forces us to ask ourselves– ‘What does it really take to secure a modern vehicle?’
Old automotive security threats remain present
Our annual analysis and breakdown of internal automotive product security data paints a picture of the complex reality– one that has unfortunately brought us to the point of manufacturers asking if existing vehicles can ever be made compliant. With so many legacy components still being used throughout the automotive industry, it’s no surprise that the automotive data shows an alarming number of known CVEs and CWEs that go along with them.
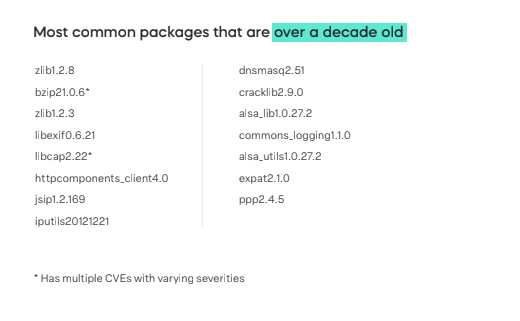
Using end of life or end of service software component packages kicks the can down the road, compounding the cybersecurity problems that will likely arise later. As new and old vulnerabilities are discovered within products, it is worthwhile for teams to identify these outdated components and consider swapping them for more secure options.
Automotive product security data in 2023 - main takeaways
In our State of Automotive Cybersecurity 2023 report, the data tells a complicated story of how critical vulnerabilities seem to stubbornly find their way into new vehicles. What OEMs like Porsche are realizing is that to sell throughout Europe (and soon beyond) they’ll have to answer to governments and shareholders for the known risks they have neglectfully allowed into vehicles.
As is now a more open secret, the automotive industry as a whole is not quite ready for the next phase of WP.29 R155 at the end of 2023– a mere 7 months before implementation. However, while there has no doubt been great progress in the world of automotive product security, there is still a way to go in terms of maturity.
Our main takeaways include
- Old threats remain persistent – Despite the greater awareness surrounding secure development, vulnerabilities are making their way into devices at a significantly faster rate than ever before. Without automation and streamlined vulnerability management and prioritization, this number seems poised to grow exponentially.
- Security is playing a bigger role – We have seen an increase in operating systems that have inherent security capabilities built in– this includes Android, up to 22% in 2023 from 18% in 2022. Another OS with noticeable growth is Debian, which is used 18.1% of the time compared to just 4.1% last year.
- Fewer private keys are being detected – There appears to be a growing awareness amongst developers and product security practitioners to use public keys and better secure their private keys. This step reduces risk to the components, should their private key become exposed.
- Developers are stuck in a ‘if it isn’t broken, don’t fix it’ mindset – The data shows reason to believe that newer software is developed securely. However, existing components that have known vulnerabilities keep finding their way into new vehicles. This is apparent through the continued presence of end of life (EOL), end of service (EOS), and no longer maintained software – introducing old risks into new vehicles.
Replacing components is a hard pill to swallow
With so many legacy components, vulnerabilities, and potentially malicious code being put into our vehicle components for years, OEMs and Tier-N suppliers have a large challenge in front of them.
No longer can they take vulnerability-packed components and keep passing responsibility down the road. Like we’ve seen from Porsche and will likely see from others, meeting WP.29 regulations are forcing OEMs to review their offerings from a product security perspective– deciding if the vehicle can be salvaged from the risk-infested environment in which it was developed to a vehicle that can remain resilient in the face of an ever-evolving and increasingly hostile landscape.
To learn more about the data that led to these conclusions and steps being taken to bolster product security maturity, read the State of Automotive Cybersecurity 2023 report.